PickleC2 is a post-exploitation and lateral movements framework
Documentation
Overview
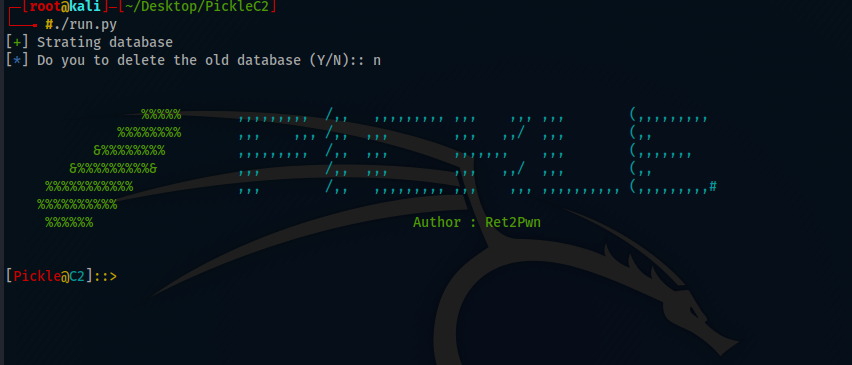
RET2pwn releasing a PickleC2 framework written in python3 used to help the community in Penetration Testing and red teaming engagements.
PickleC2 has the ability to import your own PowerShell module for Post-Exploitation and Lateral Movement or automate the process.
Features
There is a one implant for the beta version which is powershell.
PickleC2 is fully encrypted communications, protecting the confidentiality and integrity of the C2 traffic even when communicating over HTTP.
PickleC2 can handle multiple listeners and implants with no issues
PickleC2 supports anyone who would like to add his own PowerShell Module
Future Features
In the up coming updates pickle will support:
Go Implant
Powershell-Less Implant that don’t use System.Management.Automation.dll.
Malleable C2 Profile will be supported.
HTTPS communications will be supported. NOTE: Even HTTP communications is fully encrypted.
Install
git clone https://github.com/xRET2pwn/PickleC2.git
cd PickleC2
sudo apt install python3 python3-pip
python3 -m pip install -r requirements.txt
./run.py
